SIOS Product Management team is pleased to announce the general availability of SIOS LifeKeeper for Linux v 9.8.1.
New in LifeKeeper Linux v 9.8.1
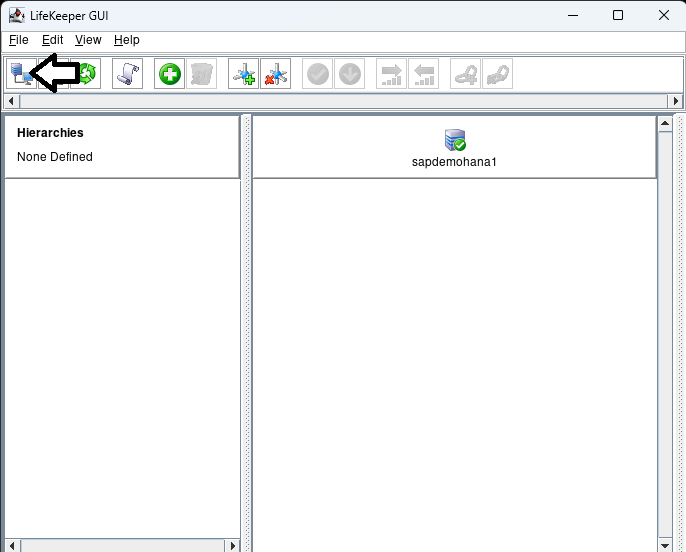
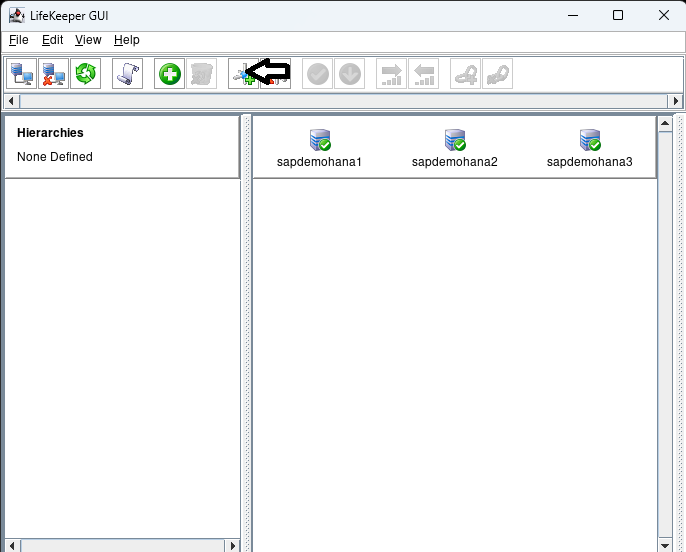
- New LifeKeeper Web Management Console Designed for Ease-of-use for system administrators in the establishment and operation phases, particularly in cloud environments. NOTE in v 9.8.1 customers can choose to run the new LWMC or the existing Java-based GUI. New features in LWMC include:
- New set up progress tracking
- New “information cues” provide self-help for all functionality
- Self-Contained – No need for additional installations or add-ons
- Language localization – Initially available in both Japanese and English language
- Simplified firewall management – access on only 2 TCP ports
- Responsive design enables use with tablets and smart phones
- Broader Support – Platforms, OS and Enhanced SAP support
- Enhanced security options
- Support for IMDS2 (Instance Metadata Service) in AWS which provides enhanced protection for programs accessing sensitive instance metadata including cloud instance ID, IP address, and the security group to which it belongs.
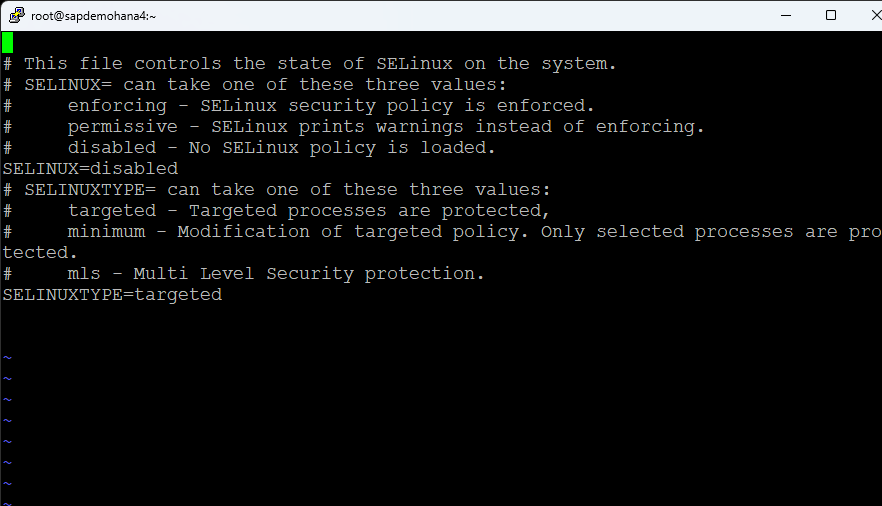
- Support for Security-Enhanced Linux (SELinux) in all three modes: enforcing, security, and disabled. SELinux provides access control to the Linux kernel as required by the U.S. National Security Agency (NSA).
- Support for additional platforms
- Fujitsu Enterprise PostGres 15
- Maria DB v10.5 – 10.11
- Maria DB v11.0 – 11.1
- Support for latest operating system releases
- Red Hat, Miracle, Oracle, Rocky Linux 8.8
- Rocky, Oracle Linux 9.2
- Rocky Linux 9.1
- Red Hat Linux 8.9
- Red Hat Linux 9.3
- SLES 15 SP5
- Support operating system versions built for enhanced SAP support SAP ARK
- Red Hat Linux 8.7
- Red Hat Linux 8.8
- SLES 15 SP5
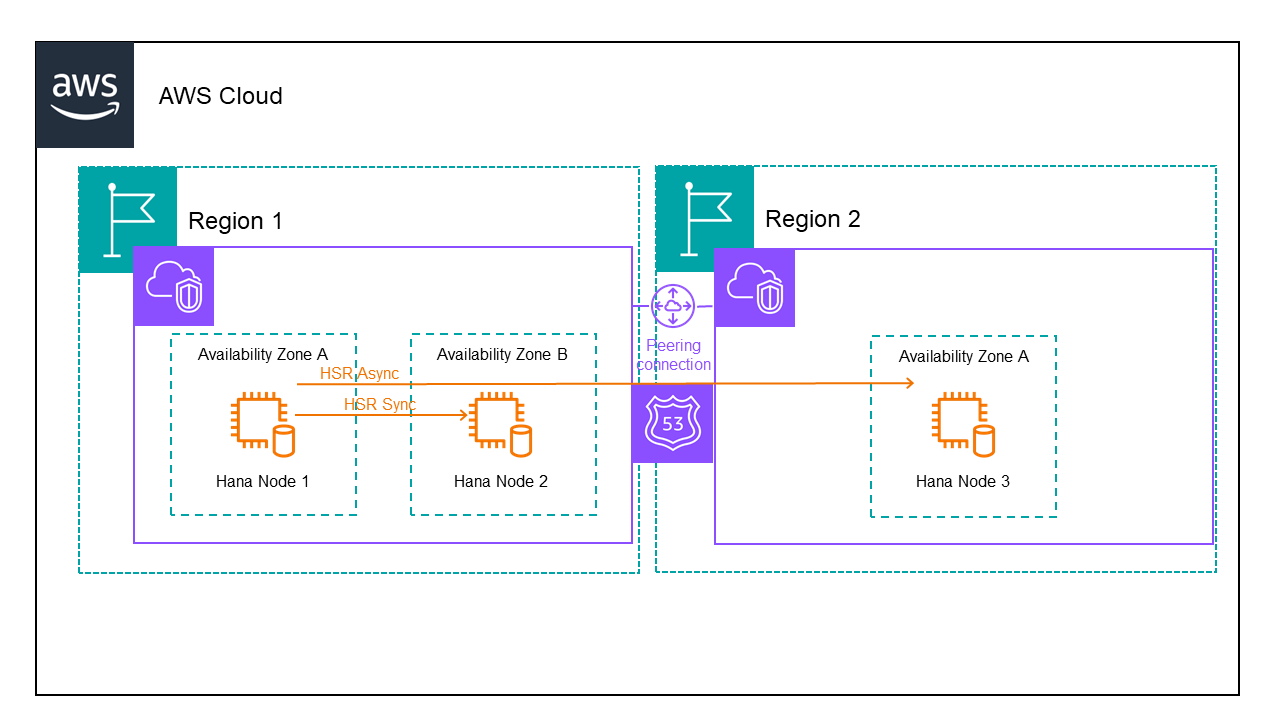
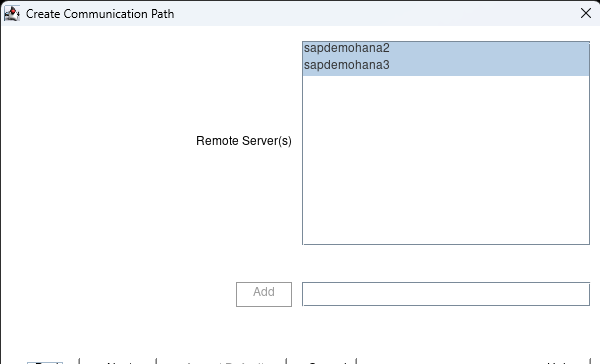
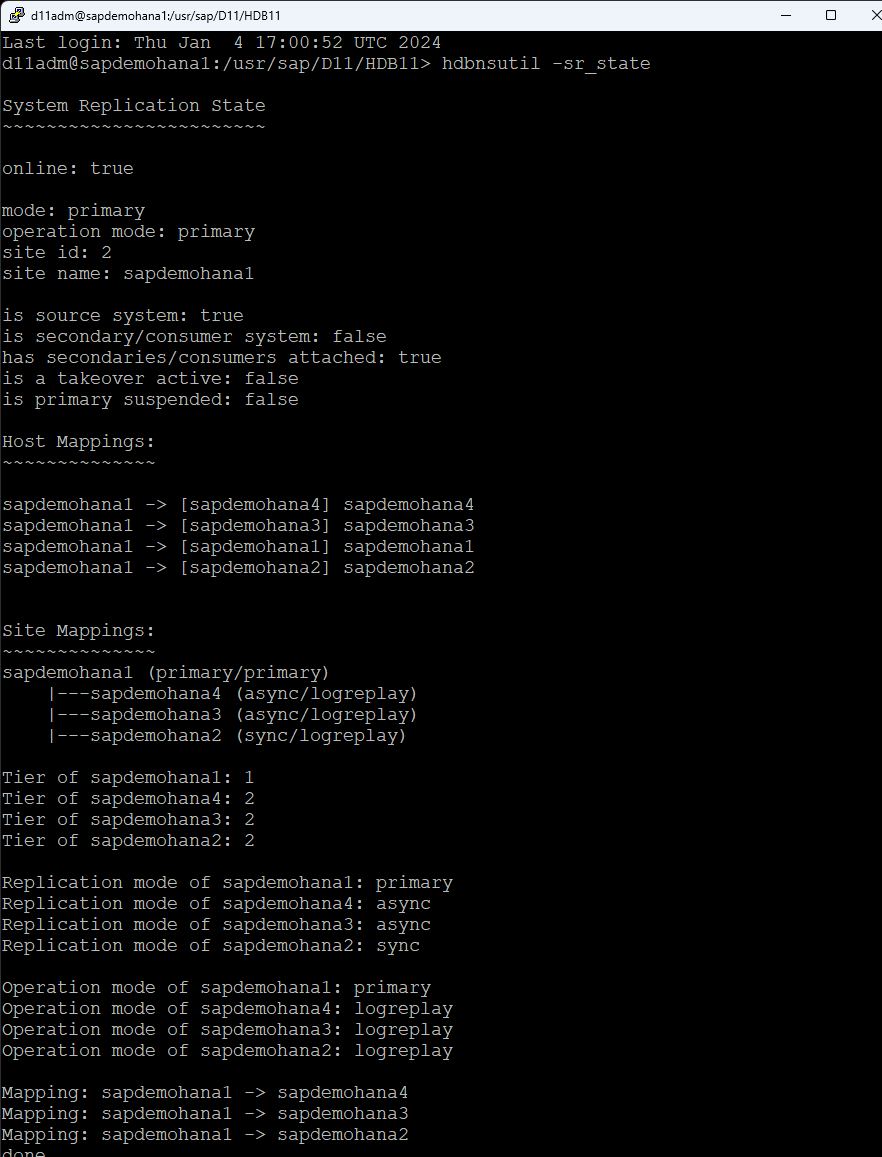
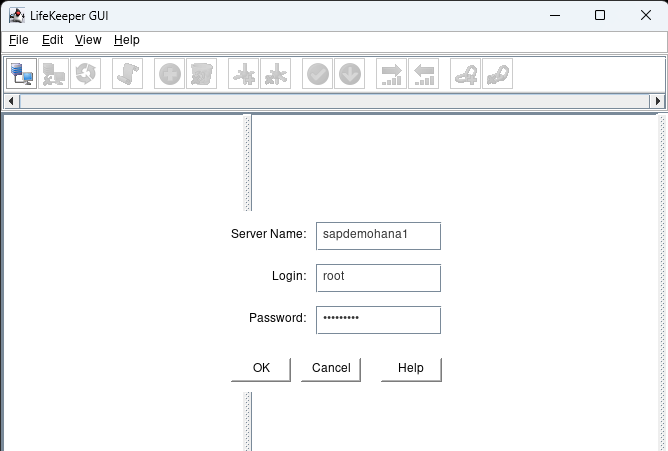
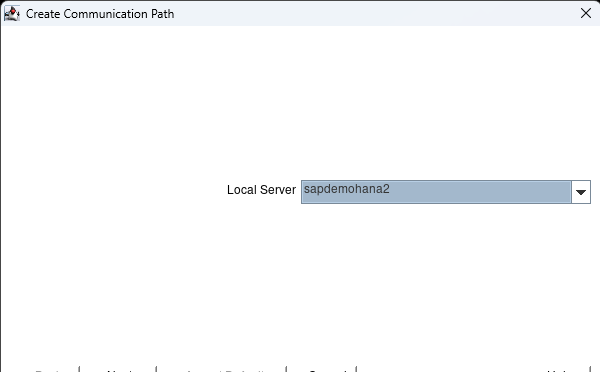
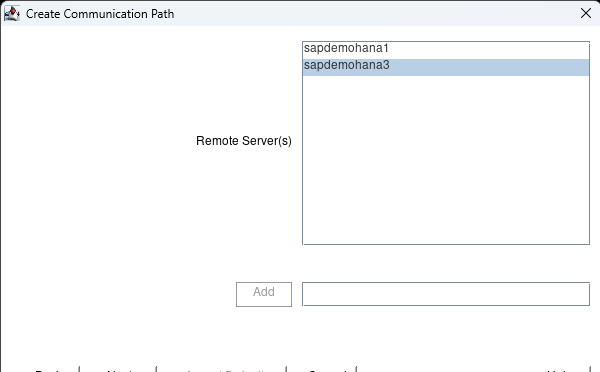
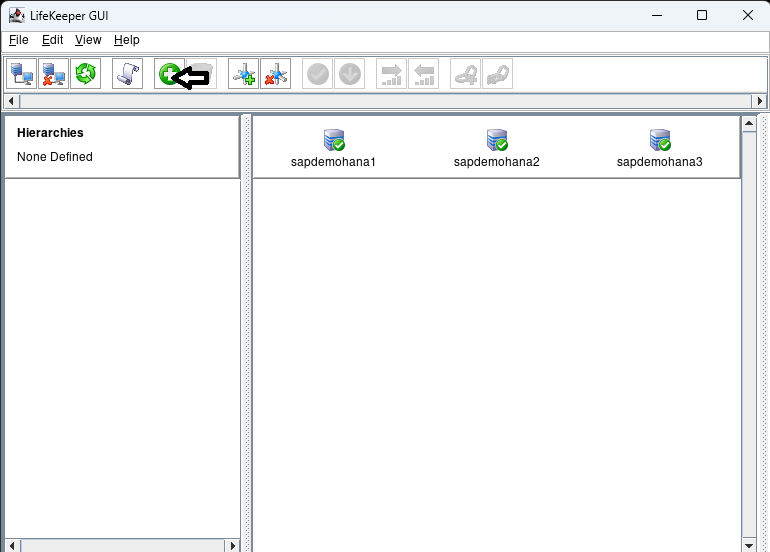
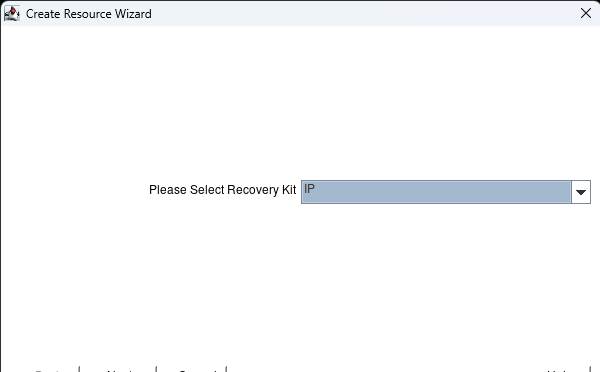
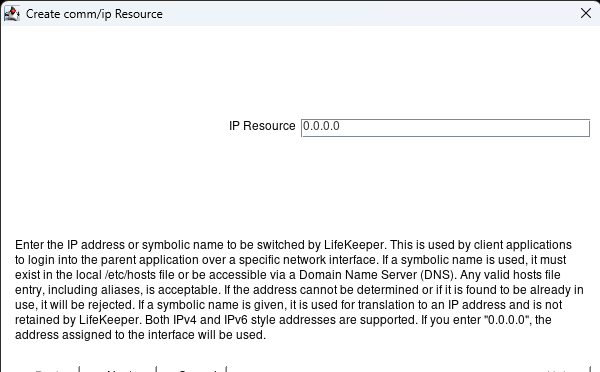
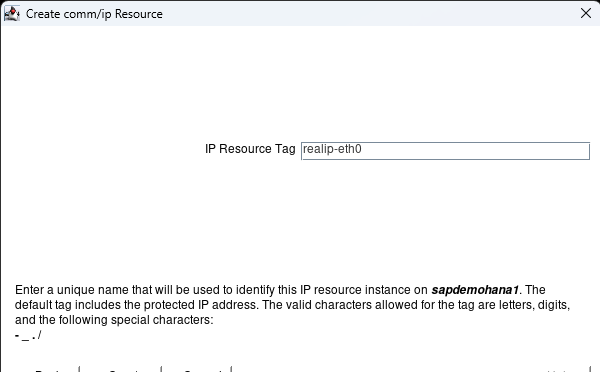
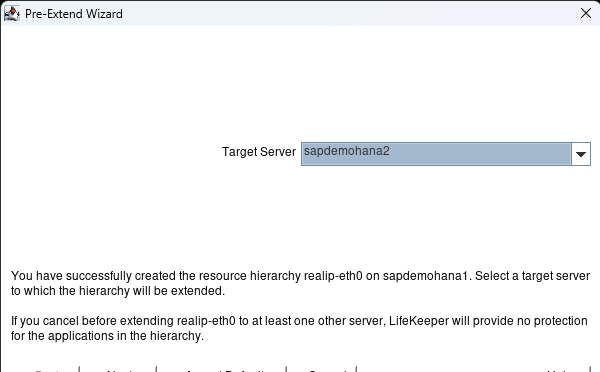
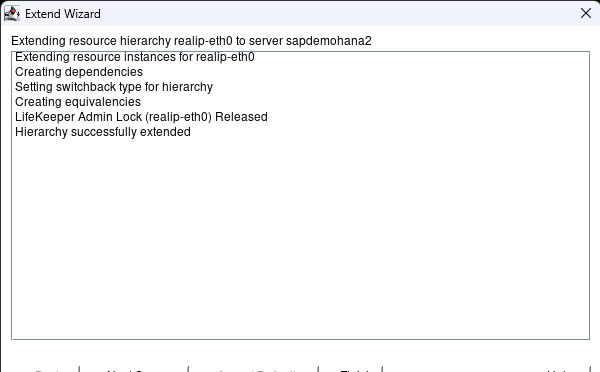
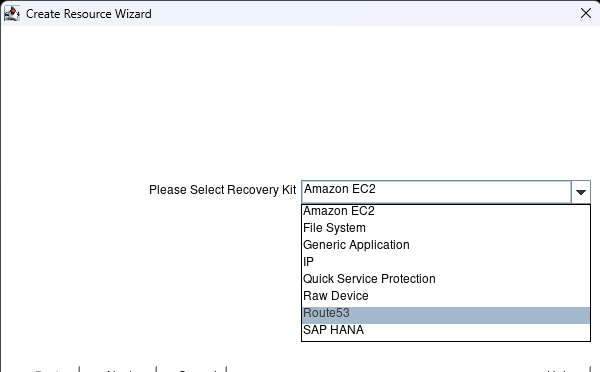
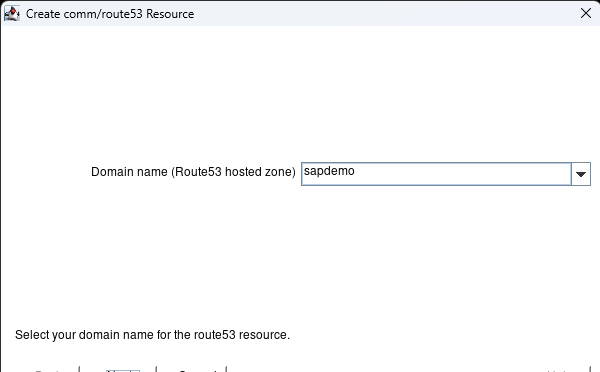
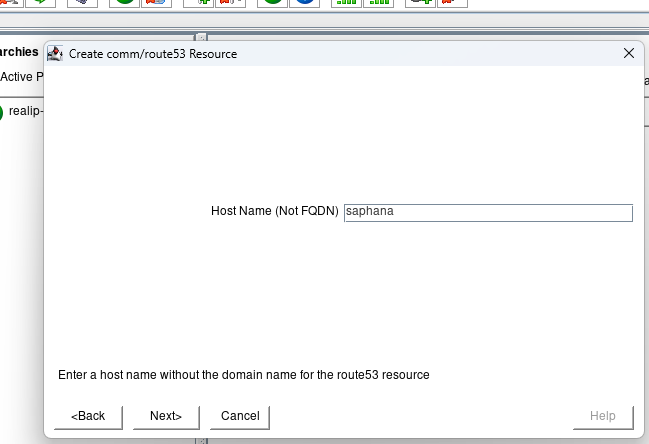
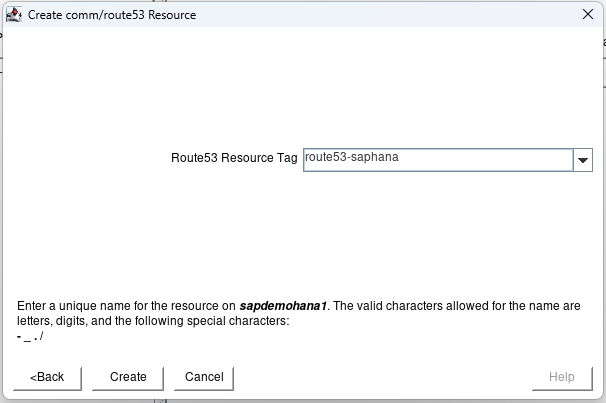
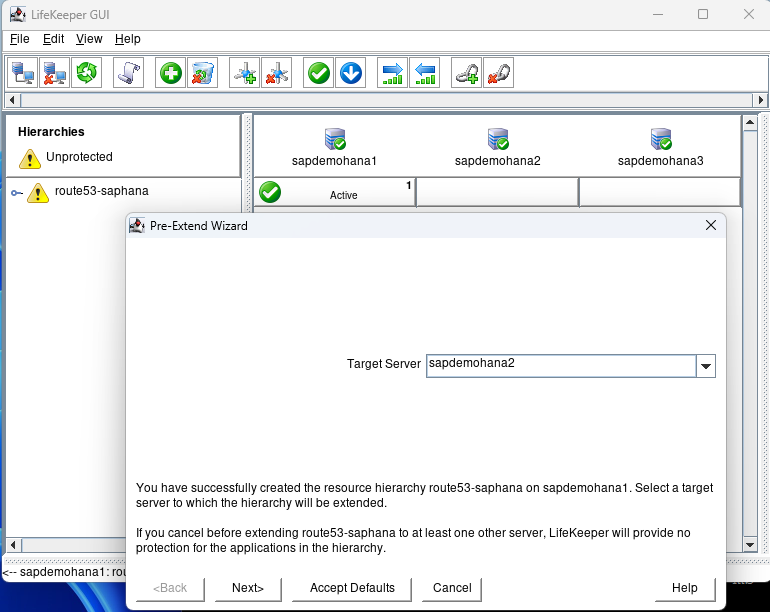
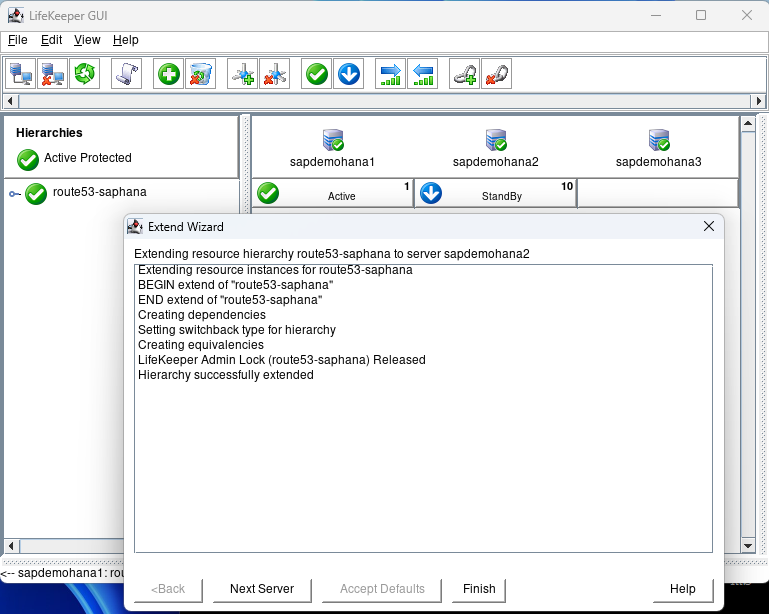
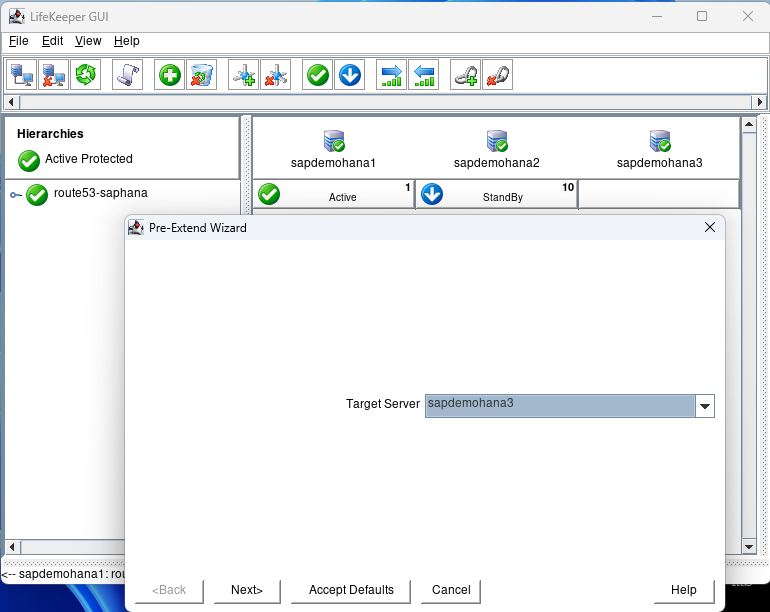
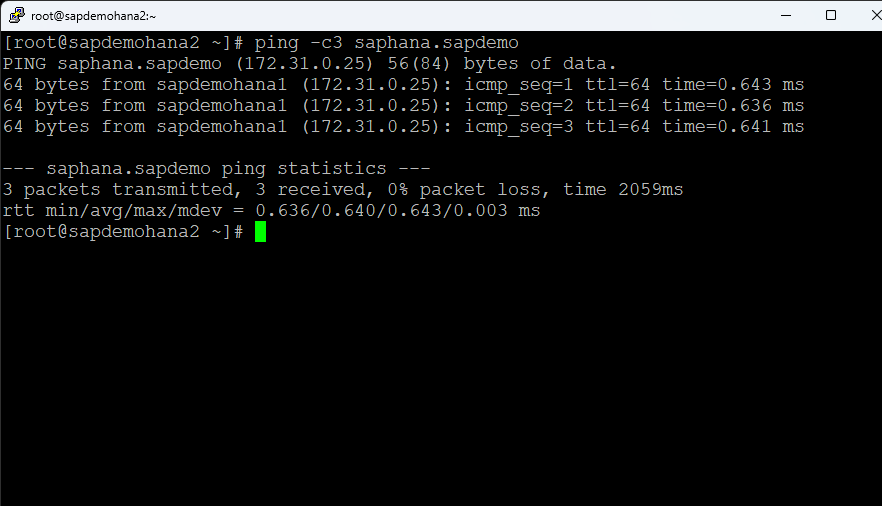
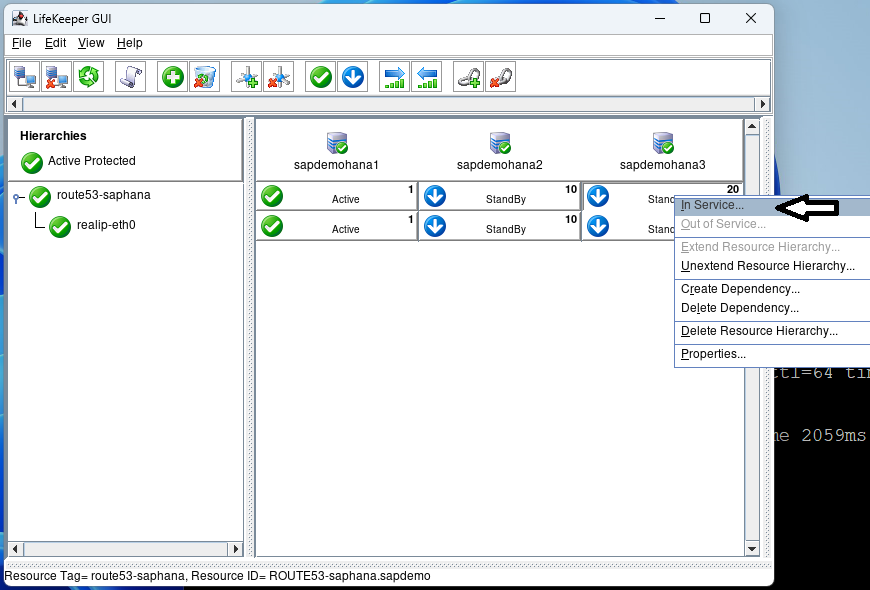
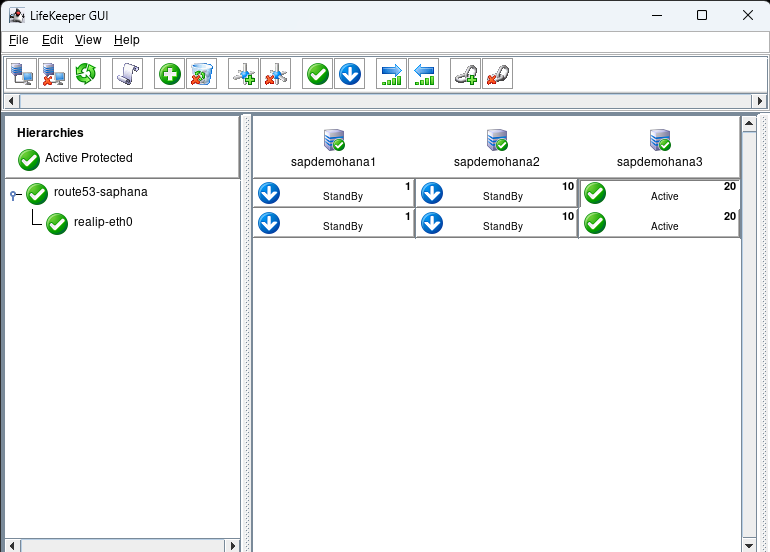
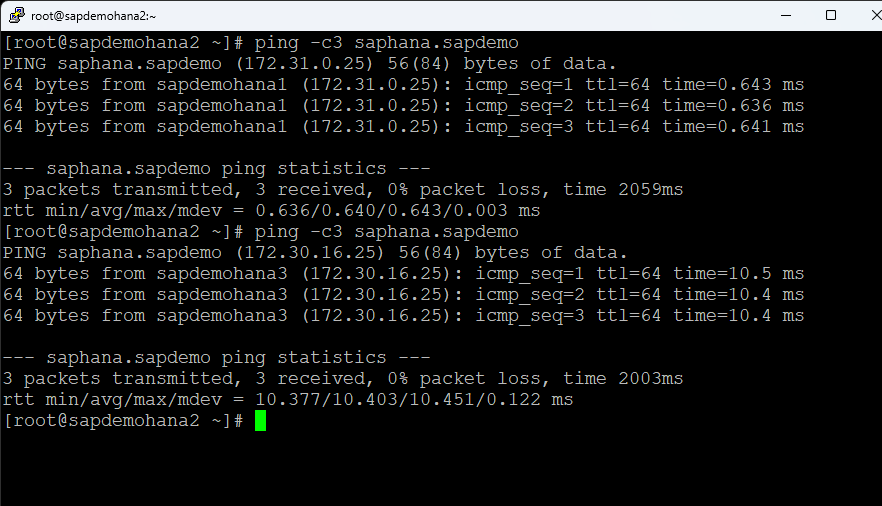
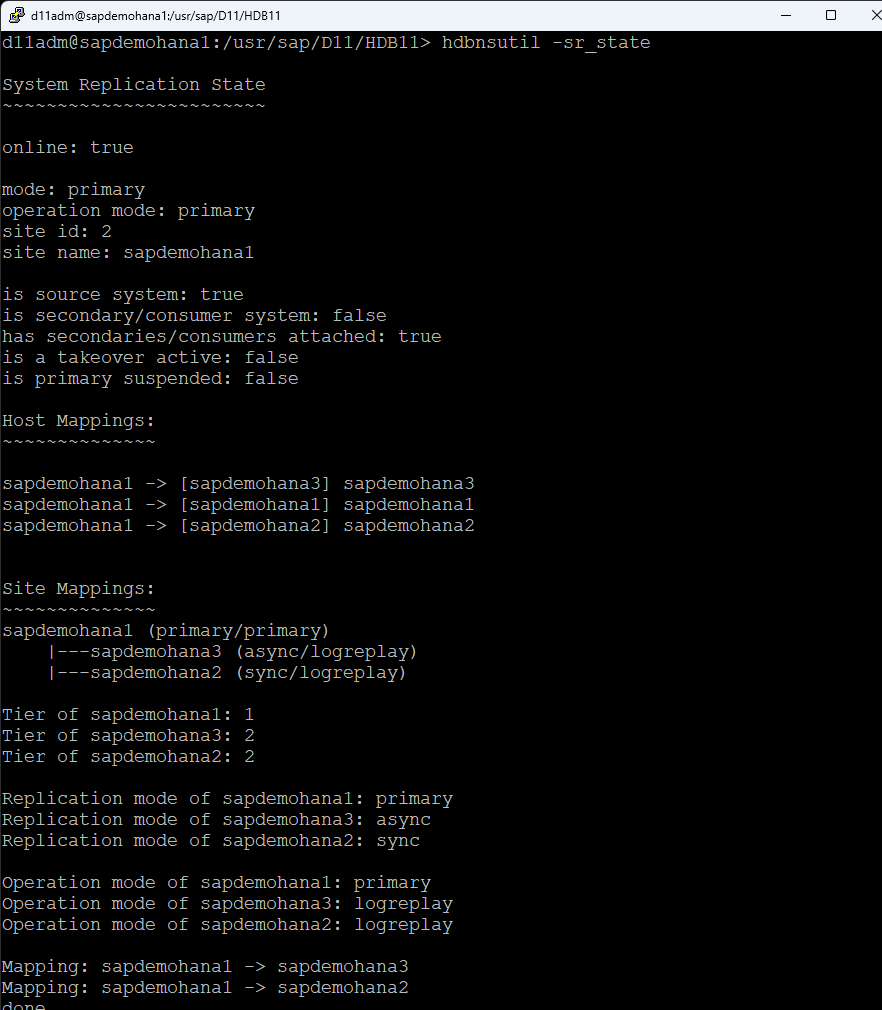
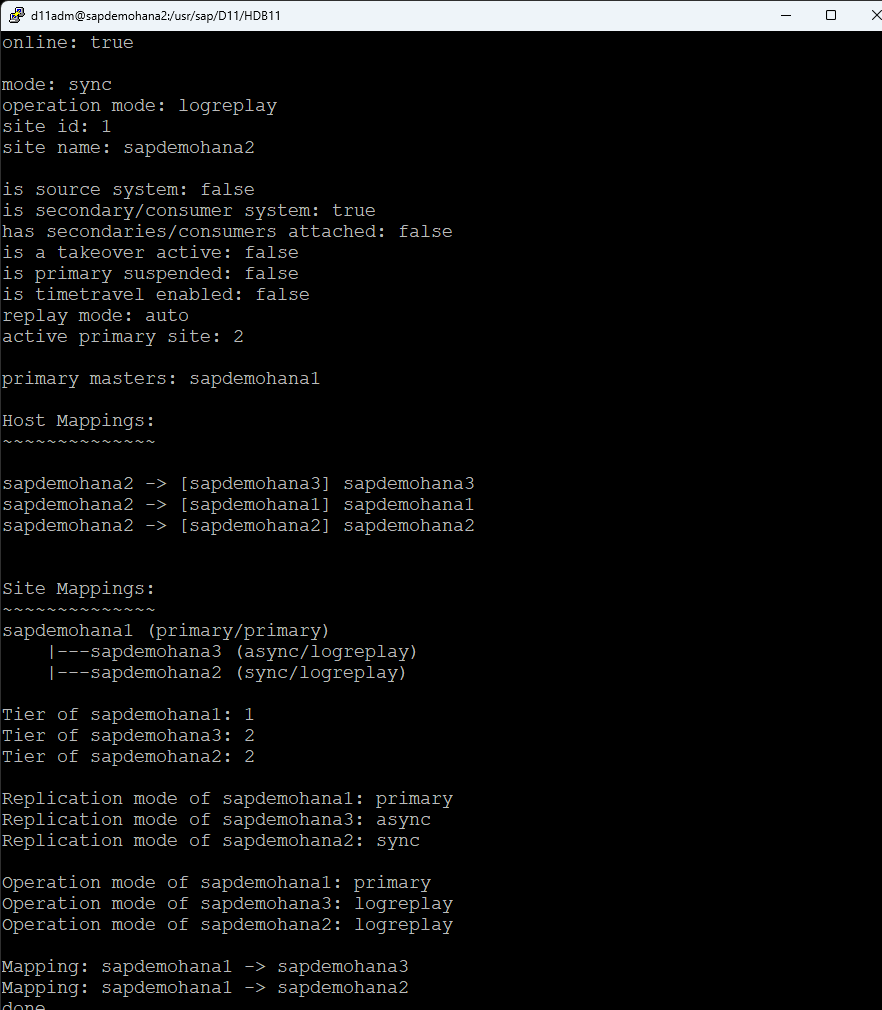
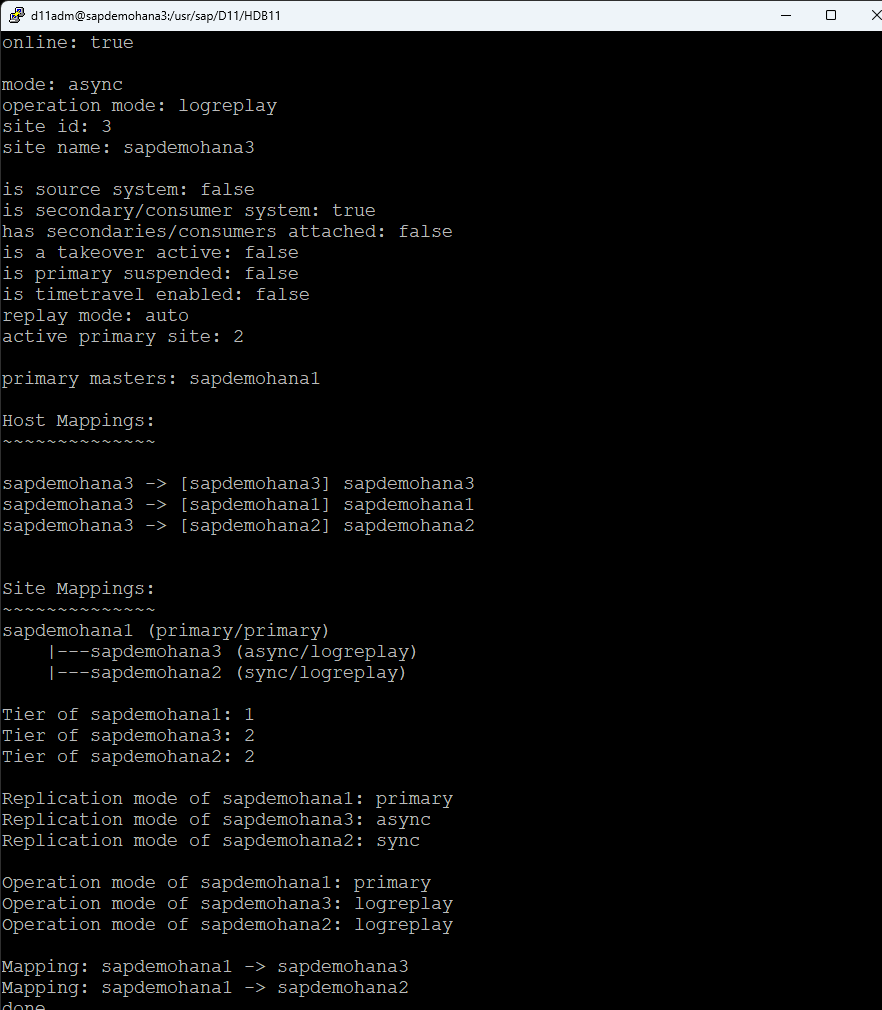
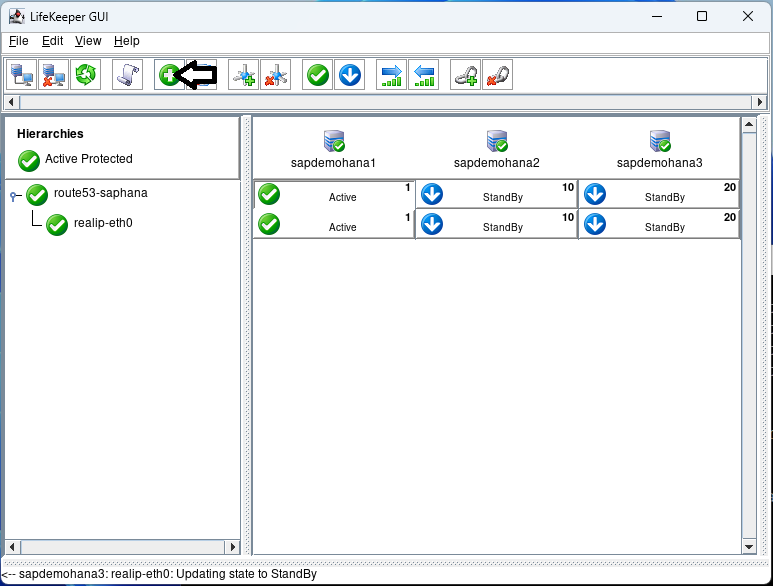
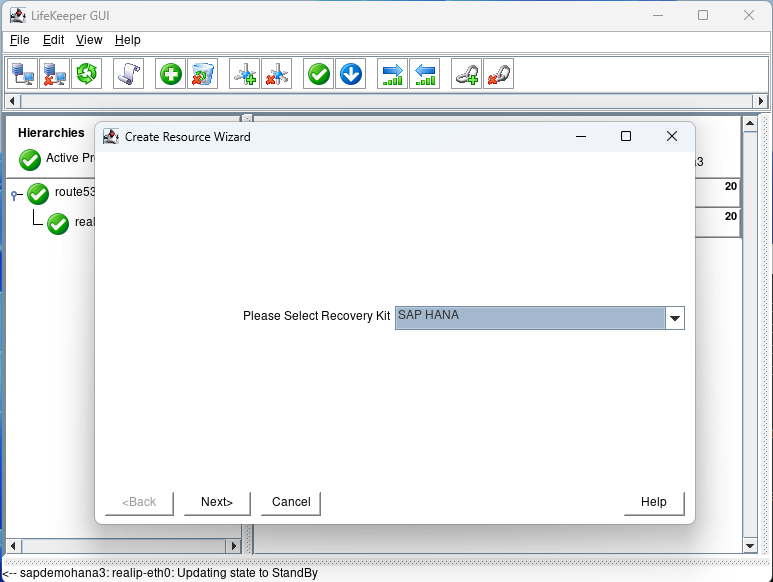
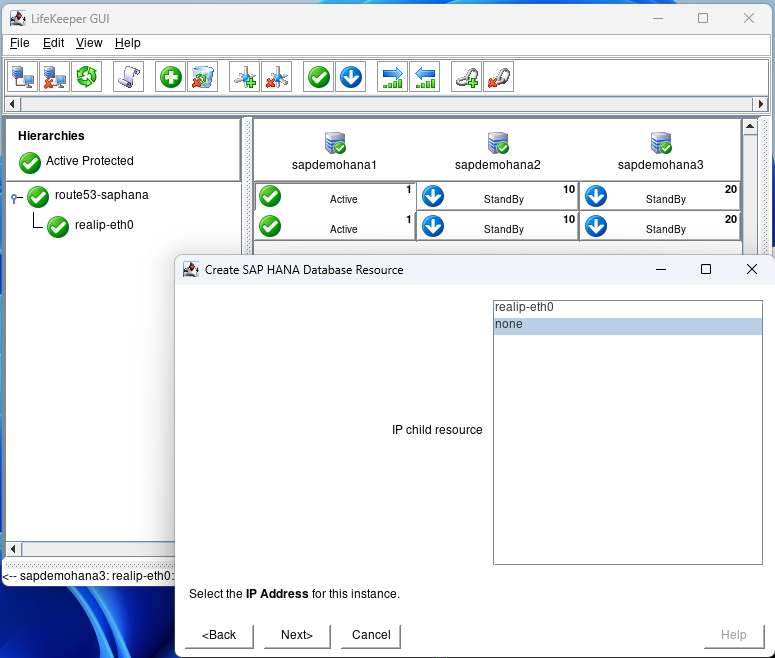
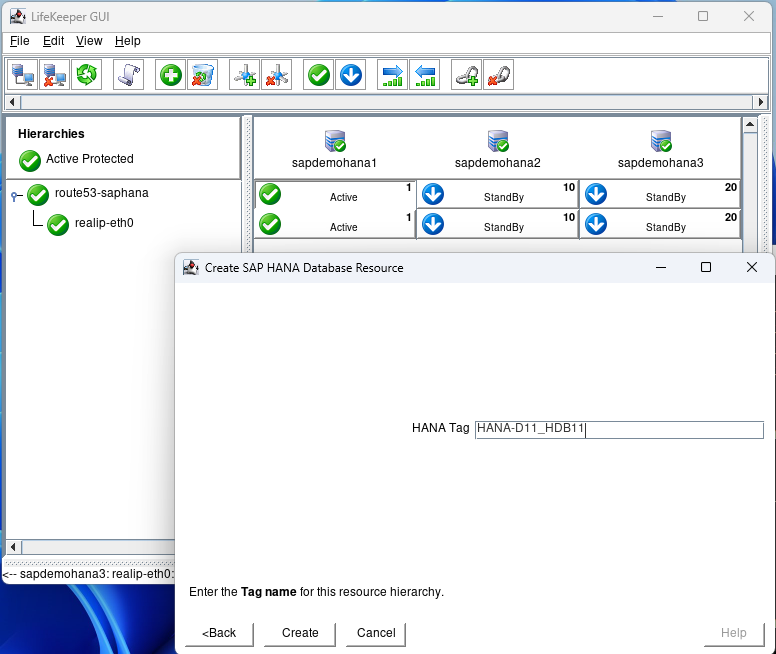
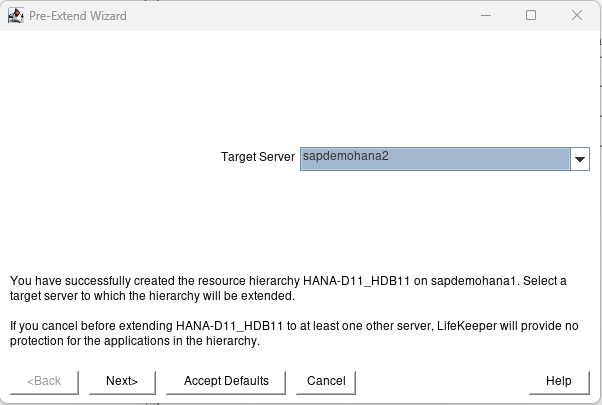
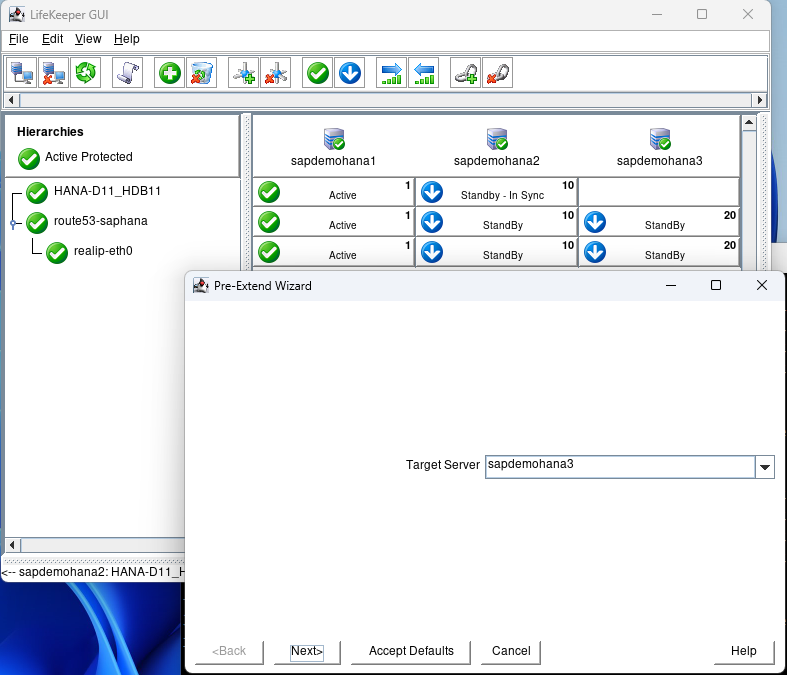
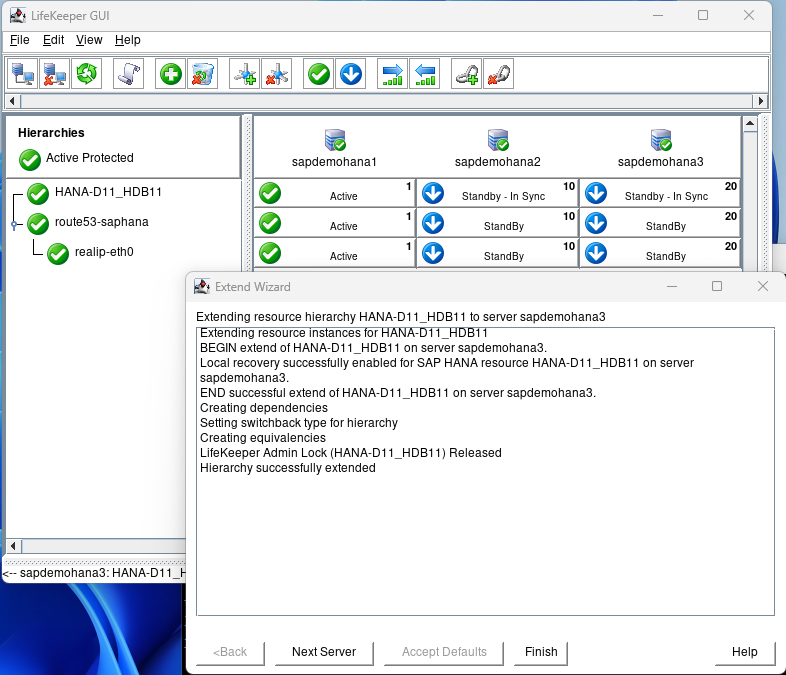
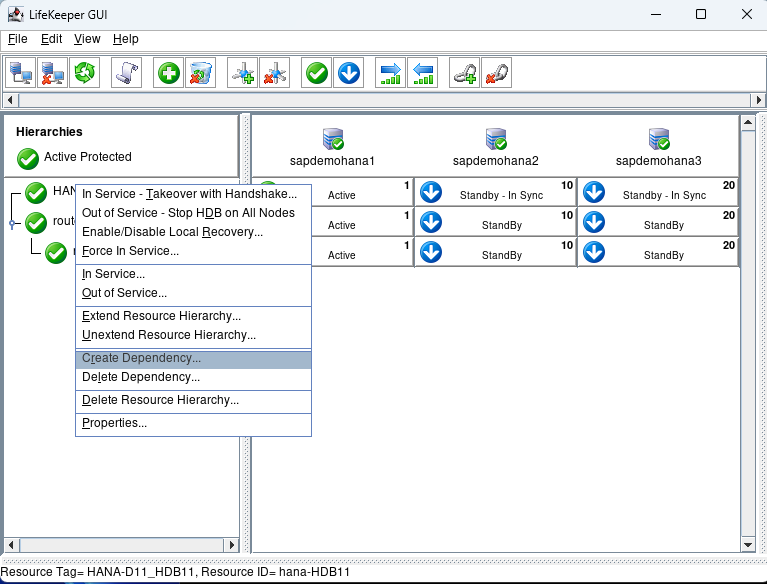
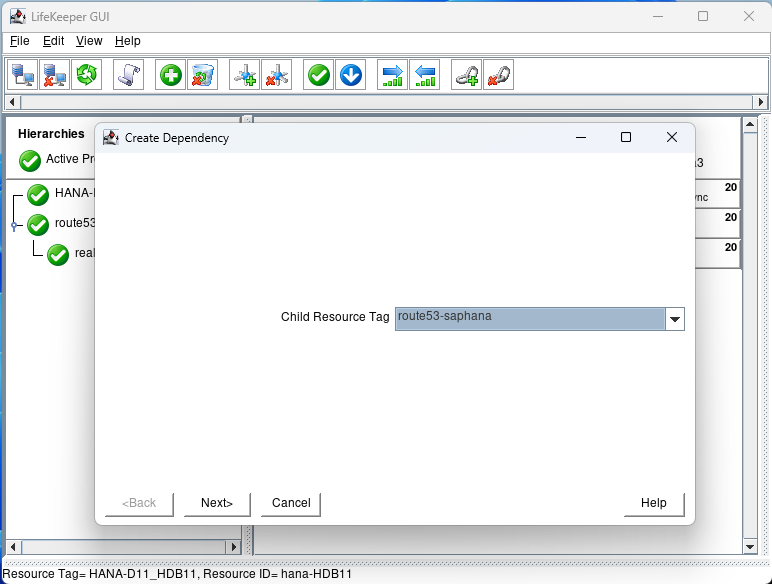
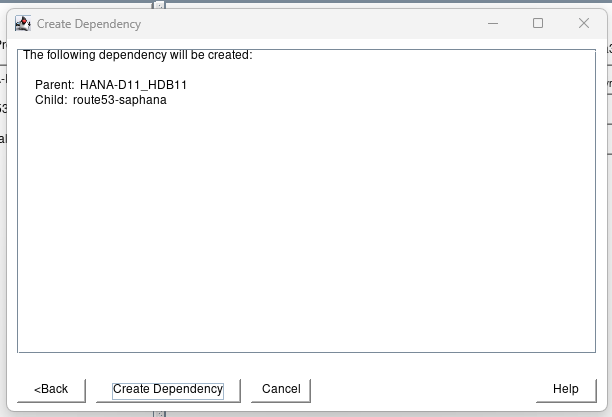
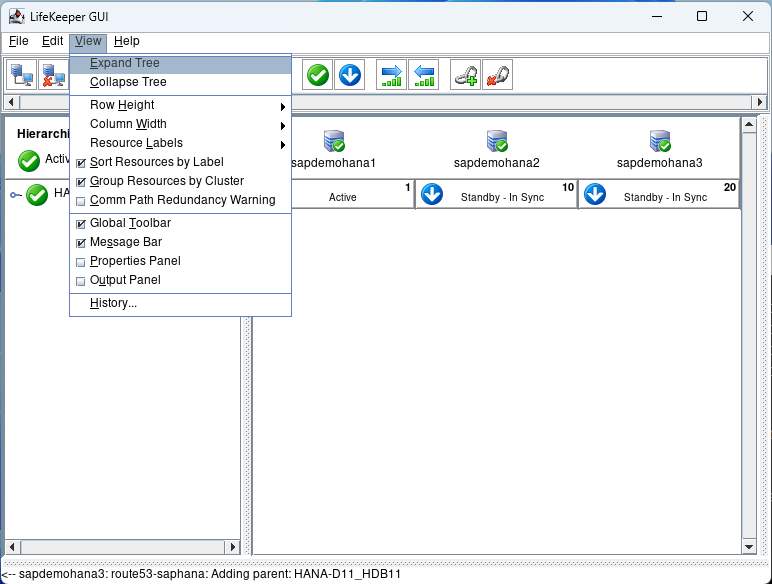
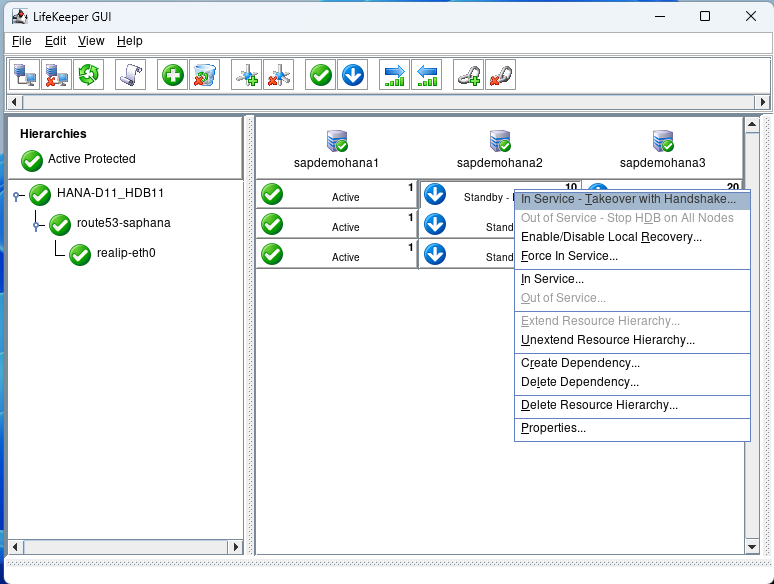
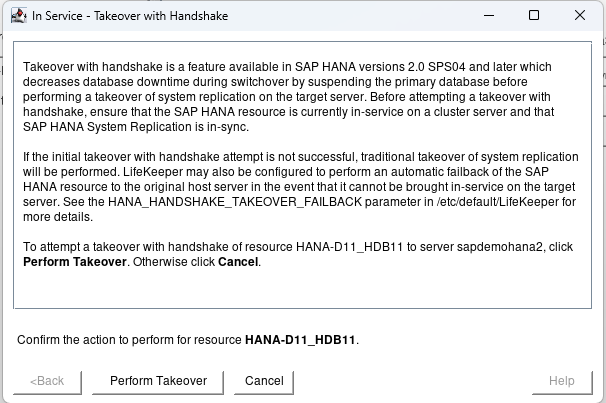
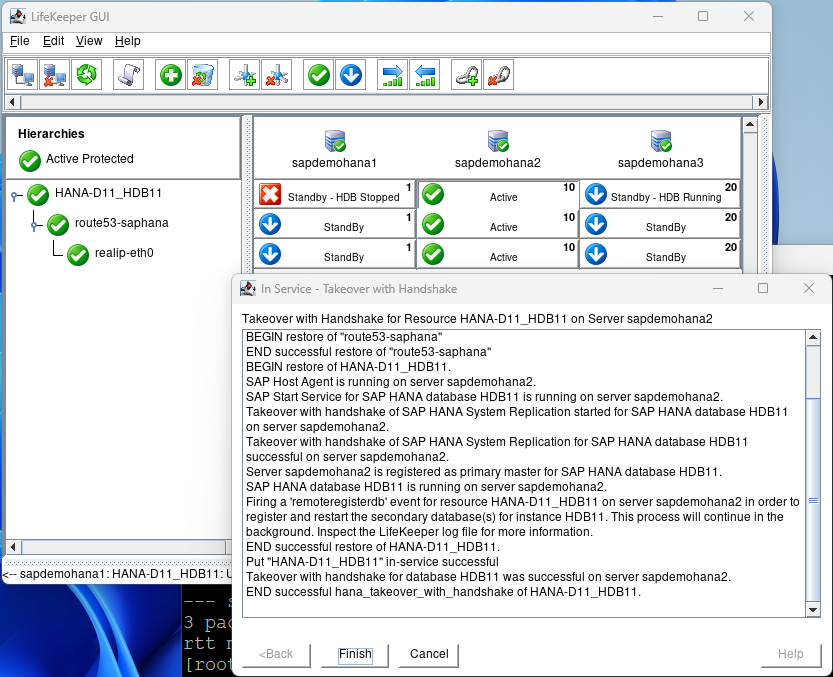
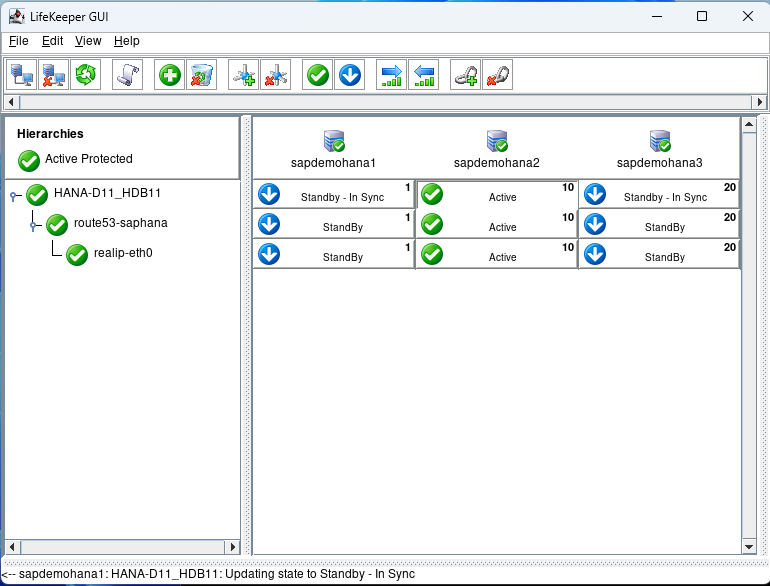
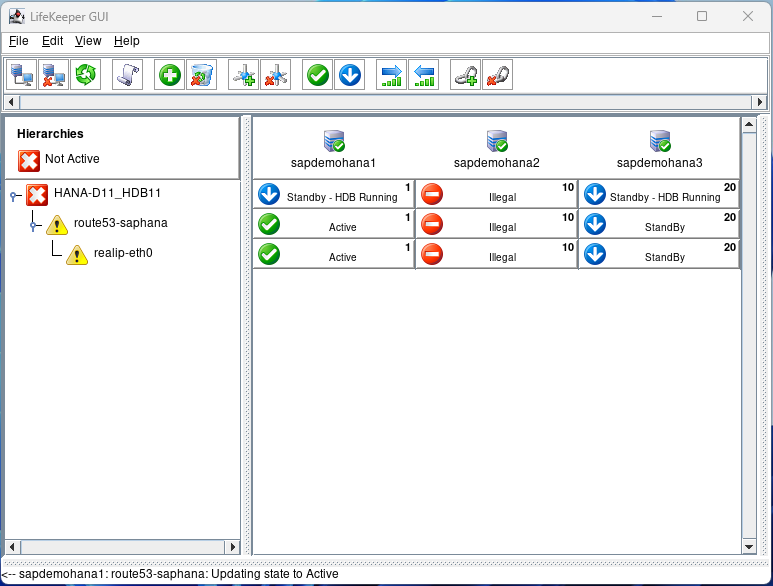
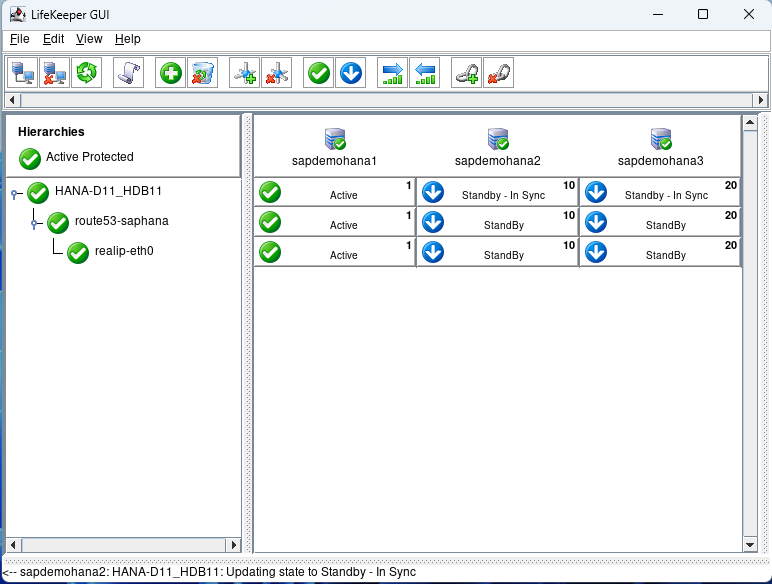
- New SIOS LifeKeeper SAP HANA Application Recovery Kit
- Red Hat Linux 8.8